The most powerful way to monitor and respond to threats in real time
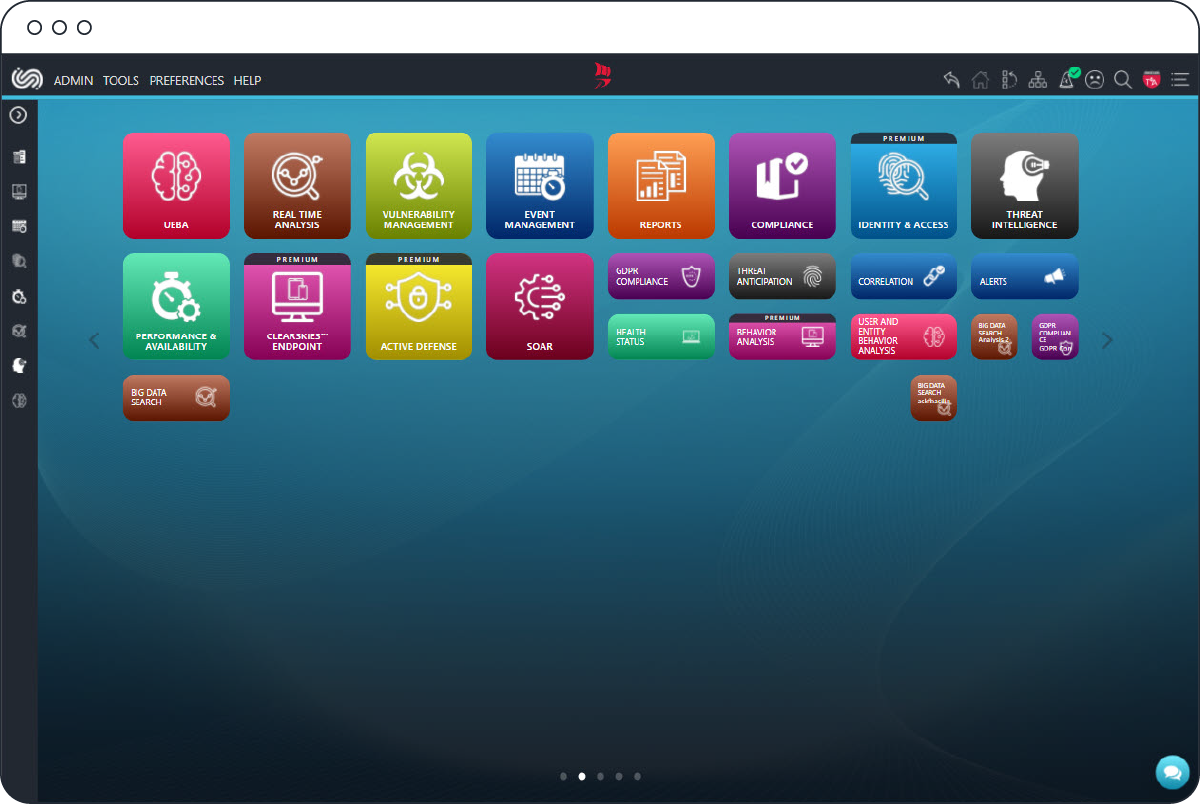
Secure Web Portal (SWP)
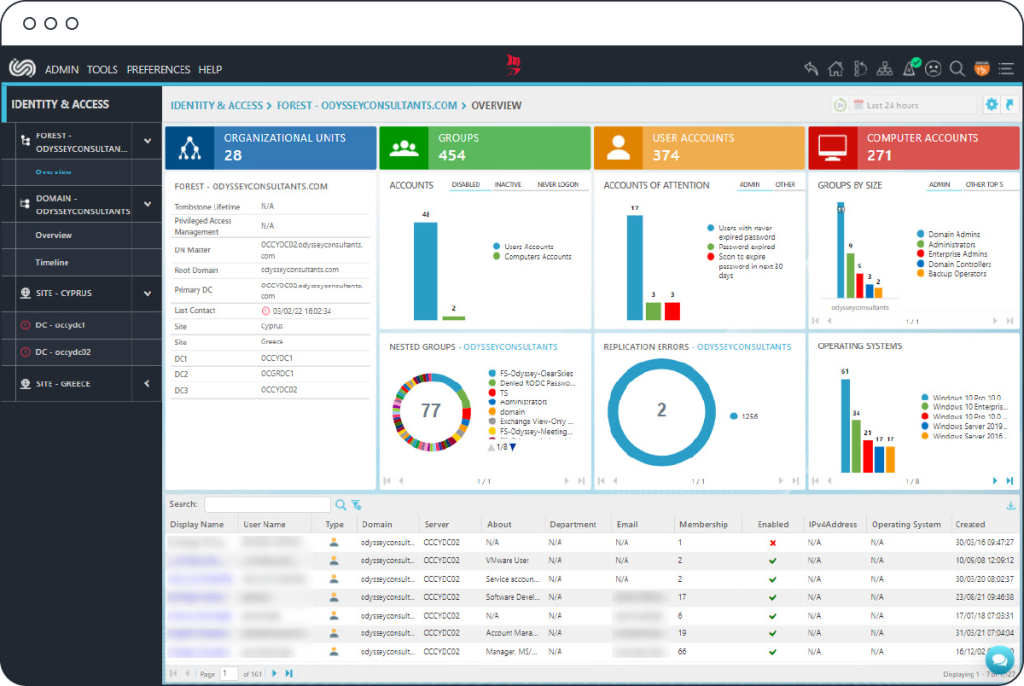
A centralized Management Console
Get real-time visibility of your security posture
Real-time visibility of your security posture made easy!
The ClearSkies™ Secure Web Portal (SWP) is a highly customizable, centralized management console, providing organizations with clear, real-time visibility of important incidents, metrics, indicators and risk assessment through smart, fully customizable intelligent dashboards.
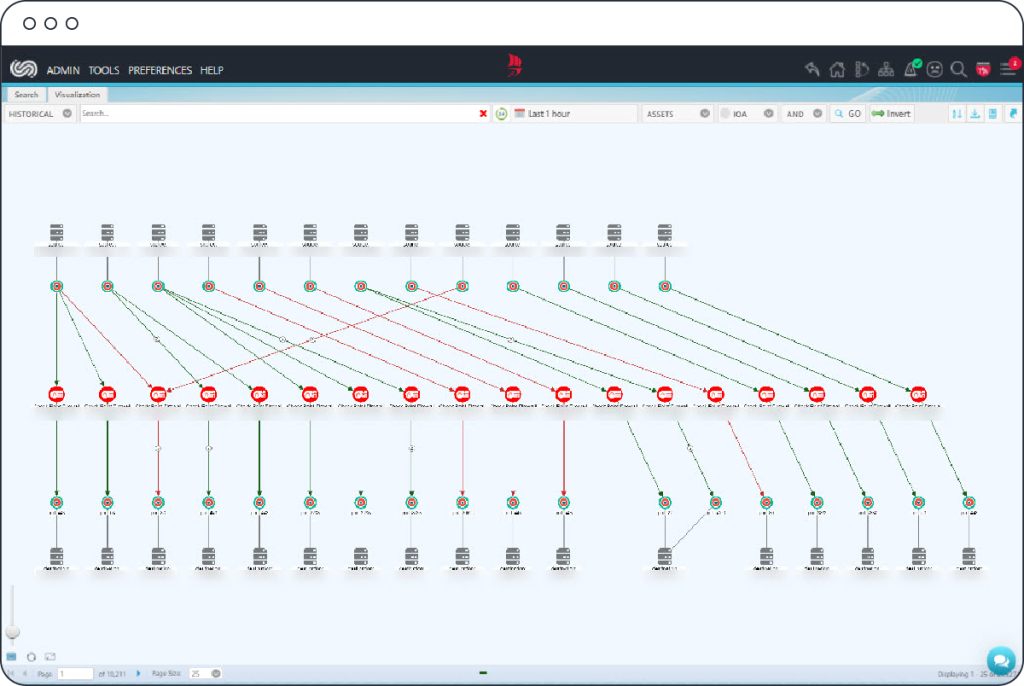
Search & Visualize
Apply simple super-fast search queries on vast volumes of log and event data collected, and review insightful meaningful visualizations of your networks’ and systems’ activity. Correlate your log and event data with Threat Intelligence to easily identify and investigate threats before it is too late.
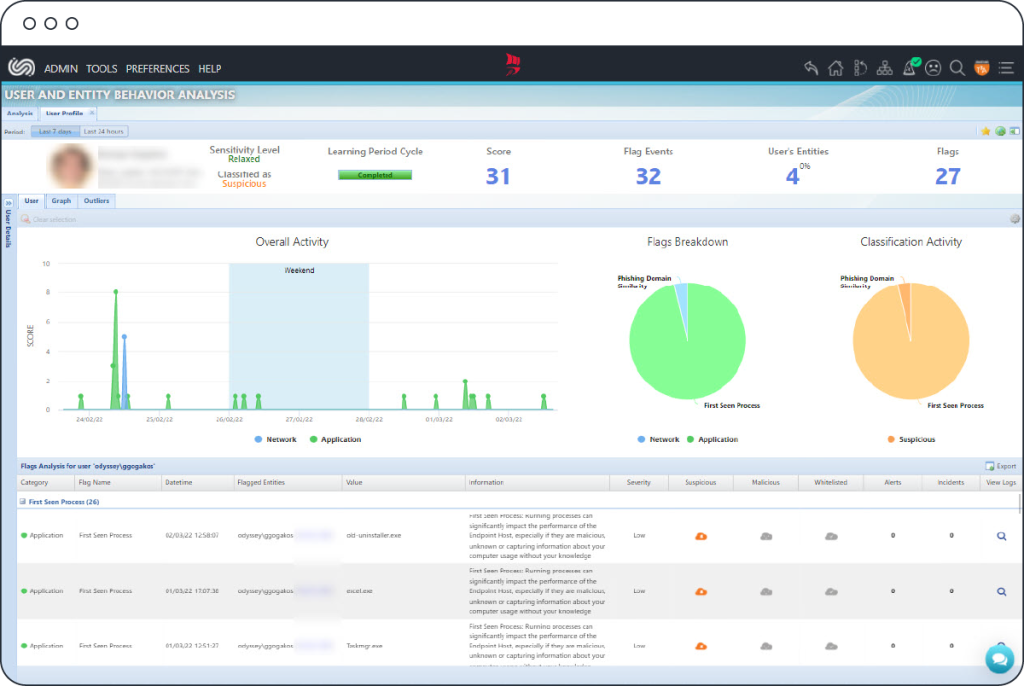
Intelligently Analyze
Deploy User & Entity Behavior Analysis (UEBA) to baseline users’ normal patterns of behavior. By constantly monitoring policy violations, configuration files, key system files, critical files/folders, network activity and running processes, you can timely detect malicious activities and/or suspicious behaviors, which could lead to data leakage, system compromise or system performance degradation that would otherwise go undetected by conventional on-premises SIEMs.
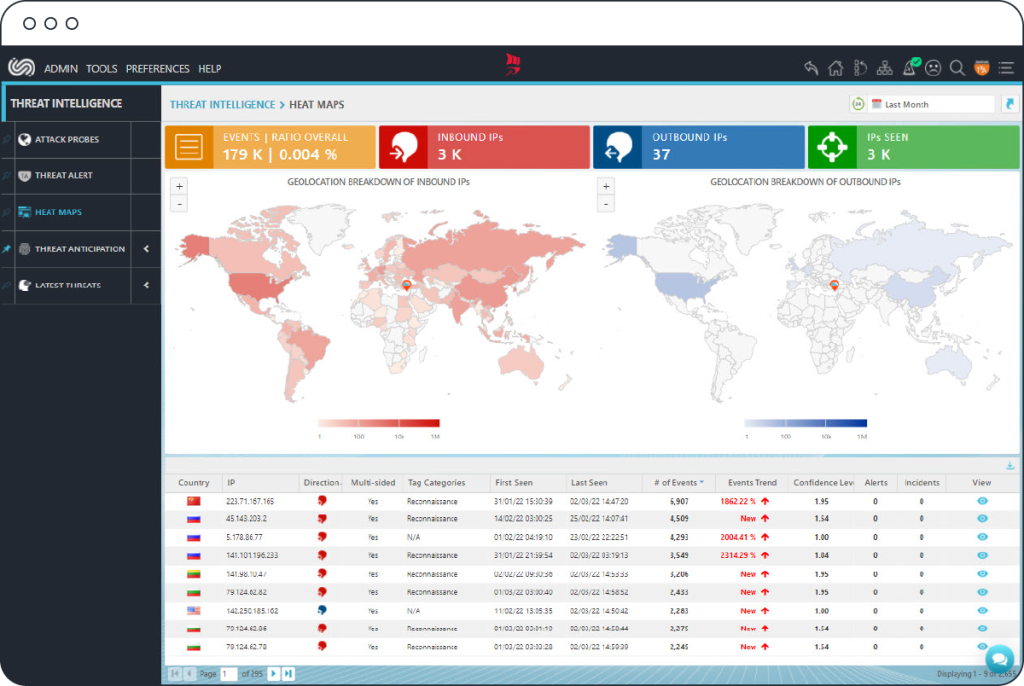
Utilize Threat Intelligence
Stay proactive against targeted attacks and data breaches by engaging evidence-based Threat Intelligence of emerging threats and vulnerabilities as they arise. Visualize the threat landscape with a near-live Threat Map and a Heat Map of threats affecting your environment. Structure your defenses accordingly in line with insightful Threat Anticipation indicators.
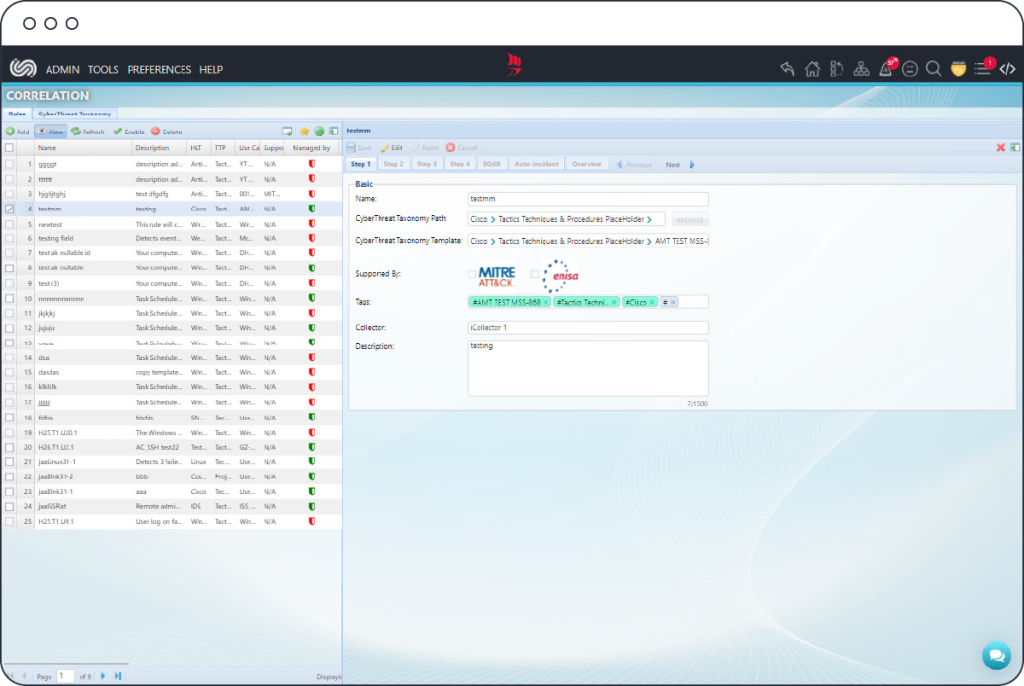
Correlate & Assess
Compile effective Adaptive Correlation Rules specific to your organization’s risk appetite, using a guided step-by-step interface. Simply assess Alerts fired according to classification and relevancy to your organization’s individual circumstances, exposures and goals.
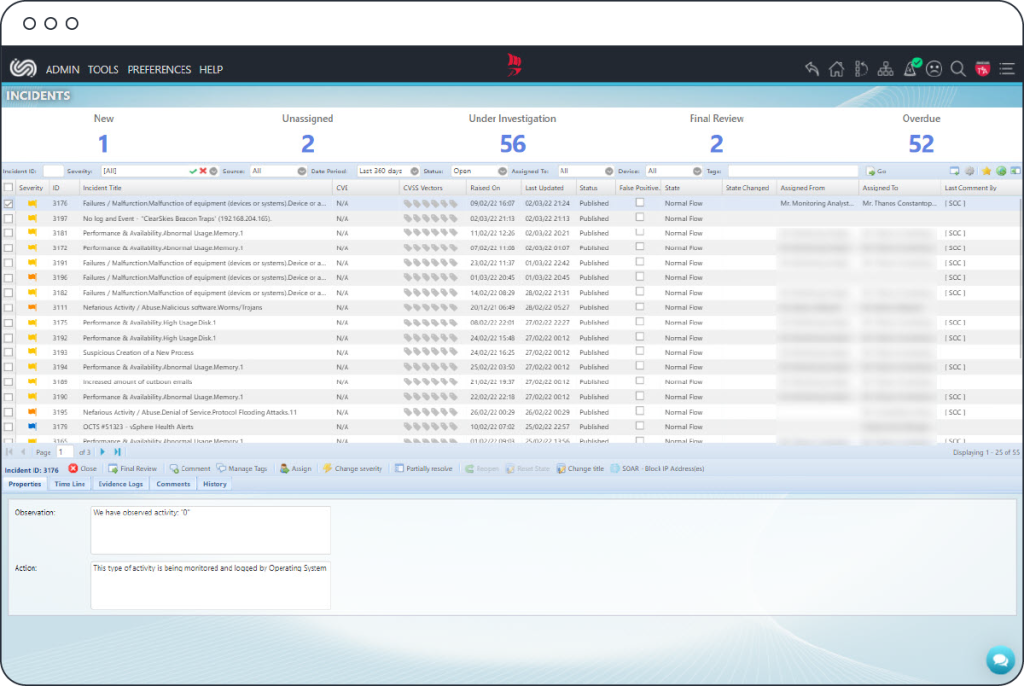
Effectively Manage
Easily assign Incidents raised to your chosen team members for further investigation and resolution. Monitor and direct the investigation and resolution progress with the user-friendly built-in management interface of the entire Incident Escalation workflow.
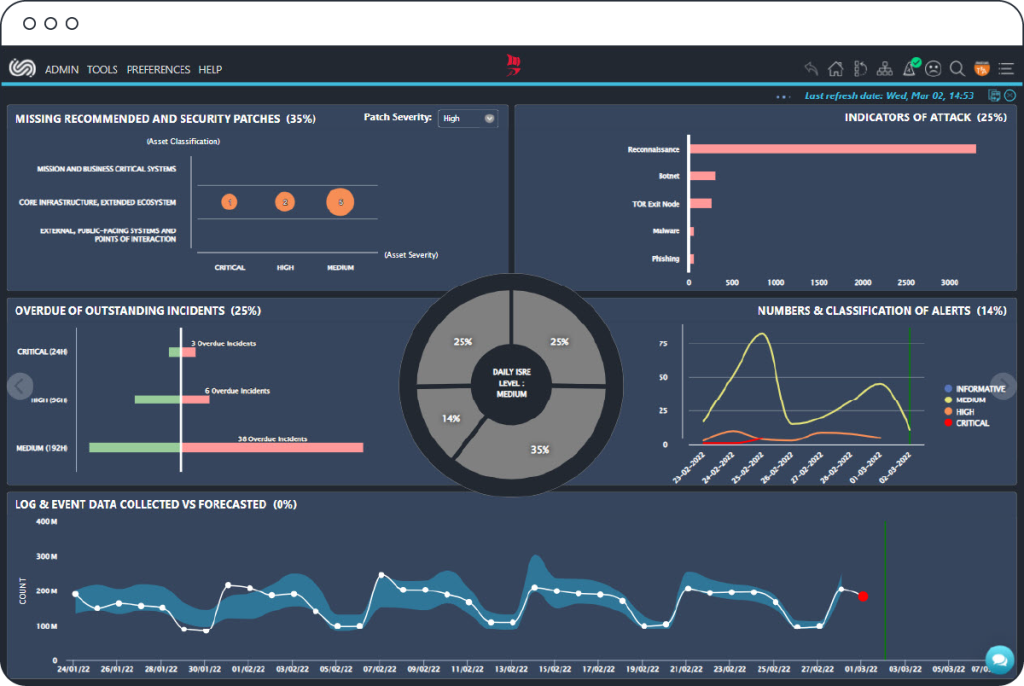
Assess Risk
Determine an indicative and precise assessment of the Information Risk to which your organization is exposed. Get a comprehensive overview of your current security posture with graphs and visualizations that accurately reflect your organization’s cyber risk level at any given time.
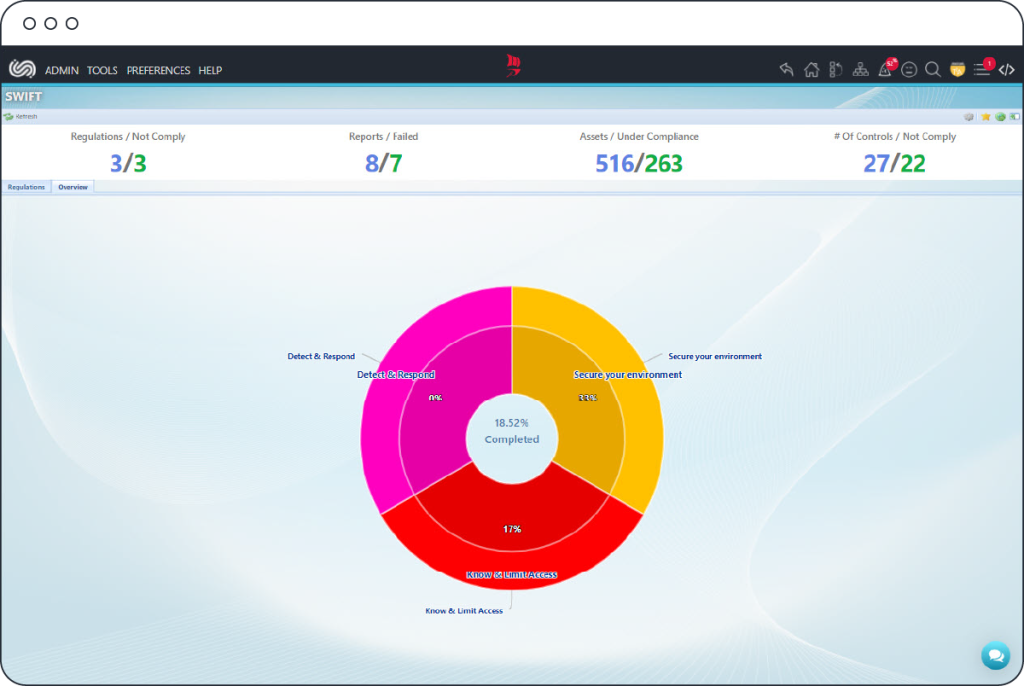
Meet Compliance
Review the exact compliance standing of your organization with comprehensive breakdowns of each regulation and its current status. Timely meet, validate and demonstrate complex regulatory compliance requirements found under PCI DSS, ISO 27001, FISMA, HIPAA, SWIFT and GDPR, effortlessly, efficiently and cost-effectively.
Monitor User Base
Stay aware of and track precisely what each user is authorized to access on your critical systems and resources. Get security alerts pertaining to identity and access irregularities.
Demo request
See it in action!
Request a live demo from our representatives to experience the value of ClearSkies™.
